The problem
I recently got the question from the customer - how to restrict traffic to the website from certain IP addresses on the Application gateway? That customer has a production website and got some suspicious requests (probably even DDoS attacks) happening from some set of IP addresses they didn't know how to block.
Question from another customer - how to let accept Application gateway traffic only for certain IP addresses? They weren't live yet and didn't want to make the website public.
The solution
After some research, I figured out Azure Network Security Group (NSG) attached to the Application Gateway subnet can be a good option to consider.
This option should be easy to configure even for the existing Application Gateway. No need to re-deploy anything or run some scary PowerShell or CLI scripts with the fear to break Application Gateway.
Basic steps to do:
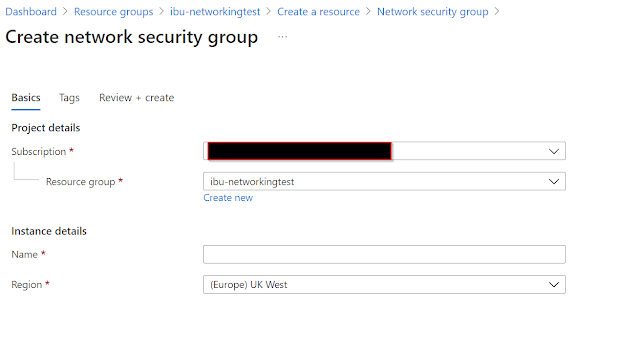
#1 Deploy NSG
#2 Configure NSG to support Application Gateway
Depending on the Application gateway version used, allow some ports on inbound traffic. See more information here.#3 Associate NSG with Application Gateway's subnet
Note: pay attention that right after you do that, you won't be able to reach the application gateway, since you need then to whitelist IP addresses.
#4 Whitelist/Blacklist IP addresses on Inbound traffic
the easiest what you can do is to whitelist IP addresses.For another scenario: blacklisting IP addresses, you should do some changes to the existing rules and allow all traffic for certain ports (for example 443). That rule should be on the lower priority than "blacklist" rules. Following is the example of the access of one IP address blocked on ports 443 and 80:
#5 Whats next
We just discussed setting rules on Inbound traffic (when requests are coming into vnet). There is an additional opportunity to set rules for outbound traffic - when request is traveling from vnet to the actual backend (Web App in my example). That gives even more options and flexibility controlling traffic flows.



Comments
Post a Comment